AWS Access Keys Access Keys are used to sign the requests you send to Amazon S3. Like the Username/Password pair you use to access your AWS Management Console, Access Key Id and Secret Access Key are used for programmatic (API) access to AWS services. You can manage your Access Keys in AWS Management Console. In this article we will describe two types of Access Keys
Root Access Keys Root Access Keys provide unlimited access to your AWS resources. It's not recommended to use them in normal situations. AWS recommends to delete existing Root Access Keys and create IAM user and Access Keys limited to specific service or resource (see below). To Delete Root Access Keys 1. Type aws.amazon.com in your web browser 2. Click My Account, Security Credentials 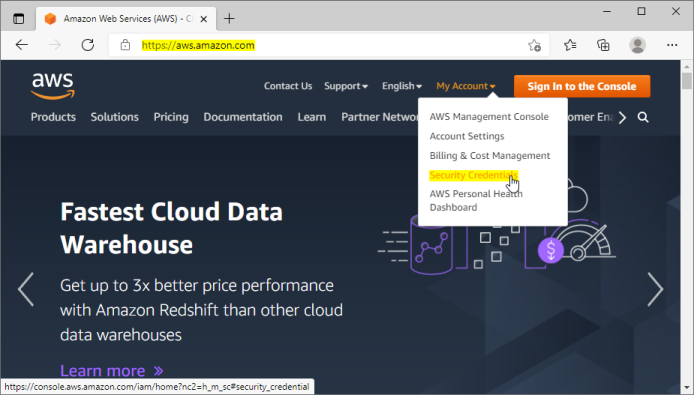
Sign in to AWS Management Console 3. Enter your account email address and password: 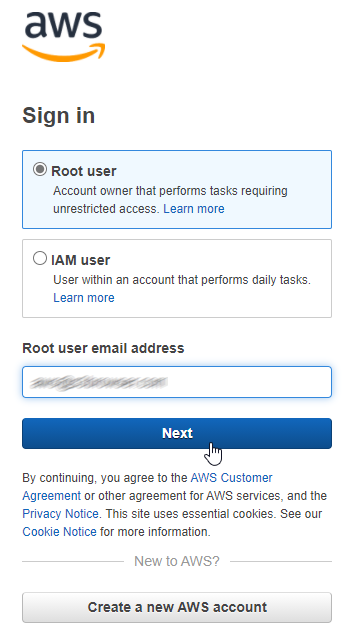
Enter Account Email 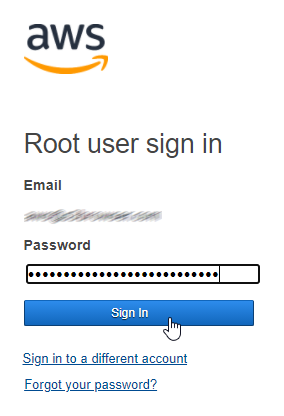
Enter Account Password You will be redirected to the Your Security Credentials page of the IAM service. 4. Expand the Access Keys (access key id and secret access key) section. 5. Click the Delete link next to your access keys. 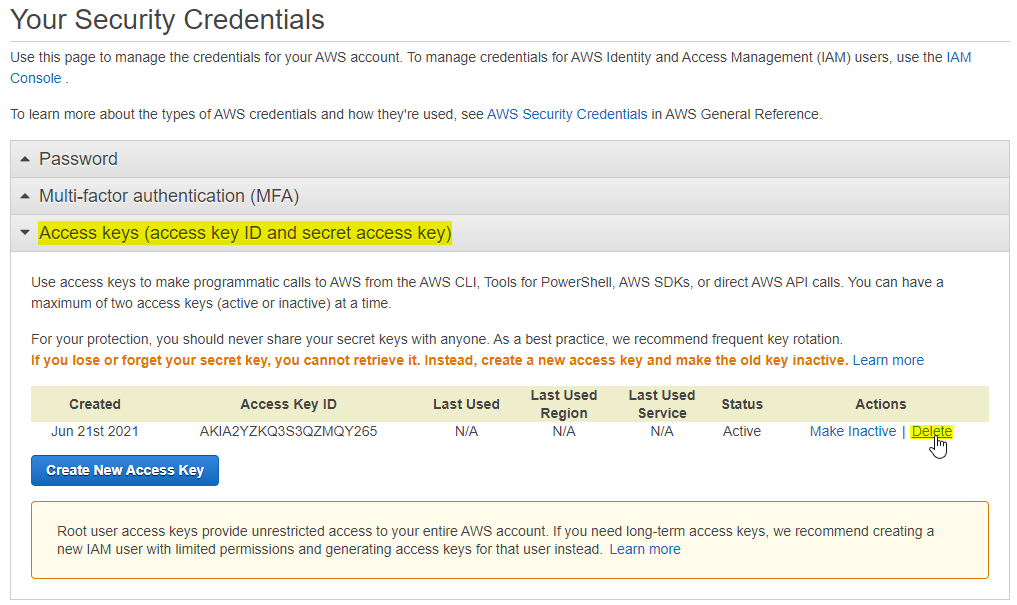
Your Security Credentials page Delete Confirmation dialog will open: 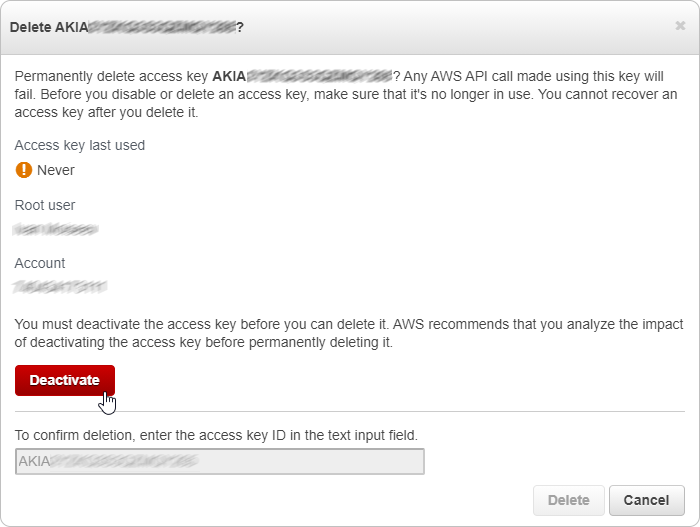
Confirm Access Keys Deletion 6. Click the Deactivate button to disable your Access Keys. 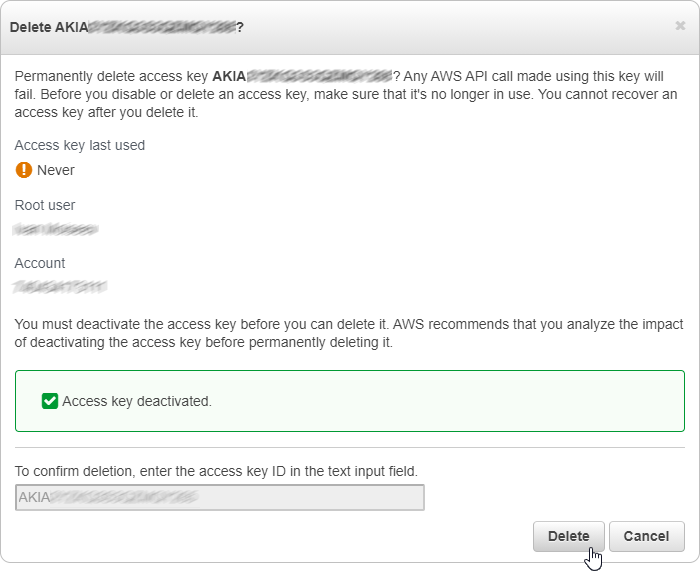
Confirm Access Keys Deletion 7. Type your Access Key ID into the corresponding text-box and click Delete. 8. Your Root Access Keys are deleted. Now you can create IAM user and Access Keys limited to specific service or resource (see below). 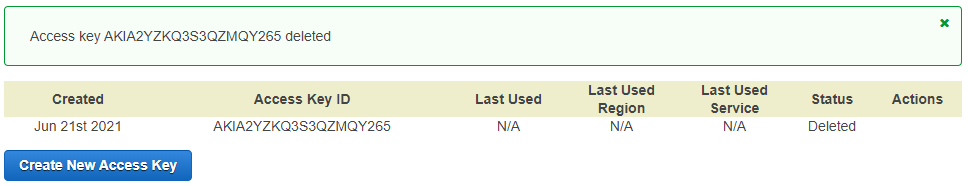
Root Access Keys Deleted Be sure to replace your root access keys with your IAM access keys in any programs/scripts you are currently using.
IAM Access Keys To create IAM user and Access Keys: 1. Open IAM Dashboard as described above and navigate to Users 2. Click Add User 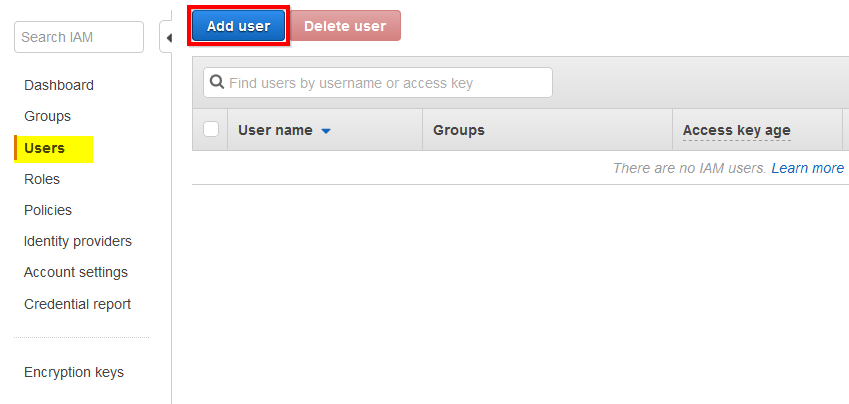
Iam Console Users Section Add User Wizard will open: 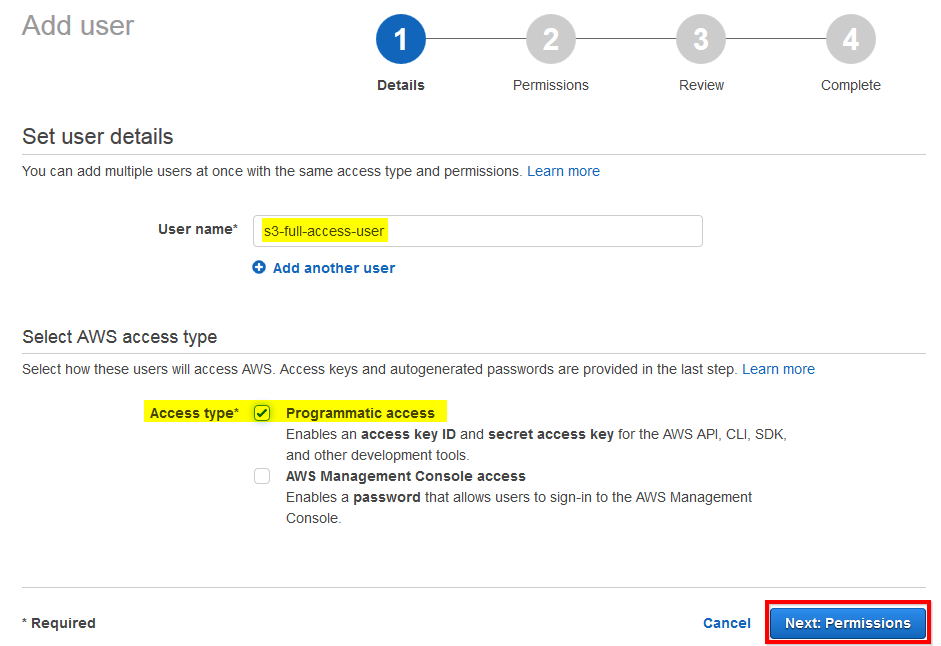
Set User Name And Access Type 3. Specify User Name (any user name of your choice). 4. Check Programmatic Access 5. Click Next: Permissions Permissions page will open: 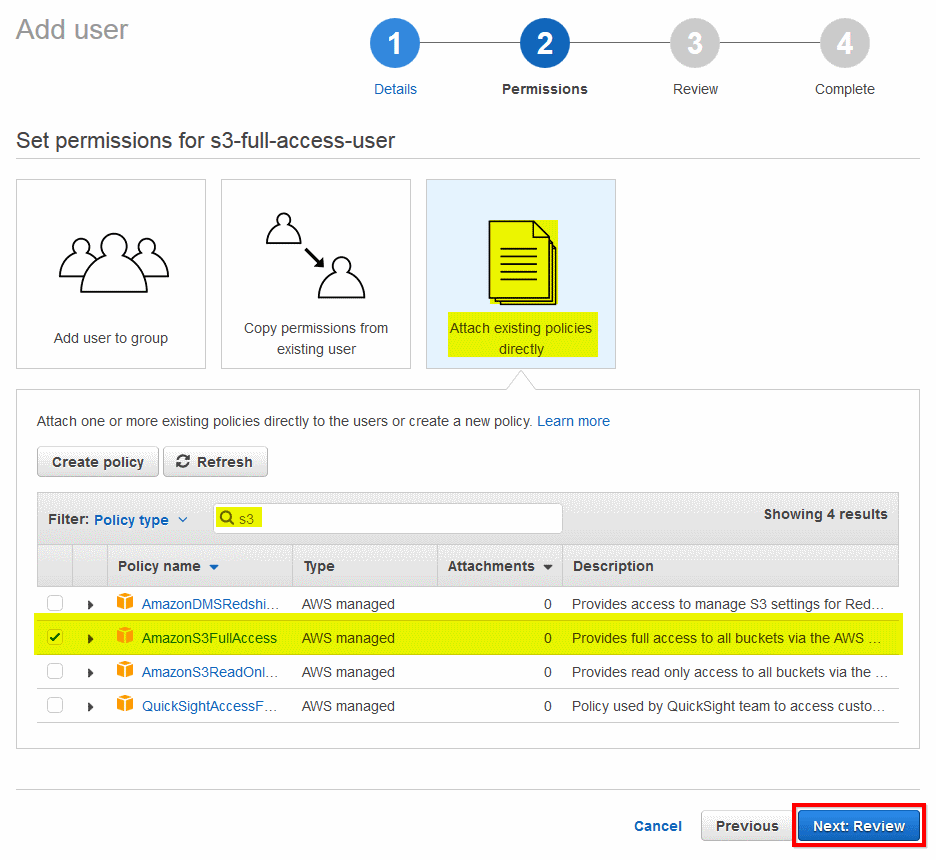
Set Permissions Attach Policy 6. Click Attach Existing policies directly 7. Type s3 in the Filter field. 8. Check AmazonS3FullAccess policy 9. Click Next: Review Review tab will open: 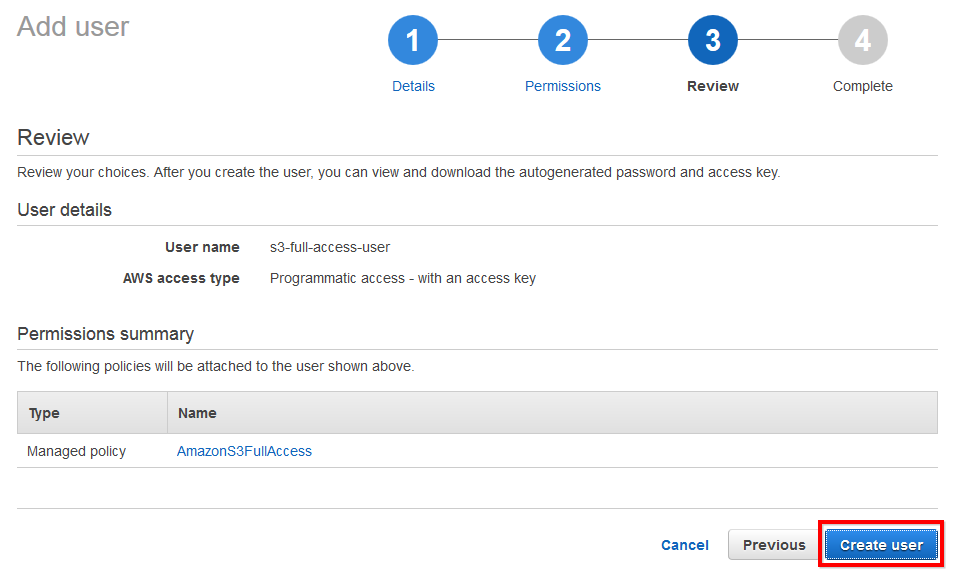
Create User Review 10. Review new user details and click Create User The final page will open: 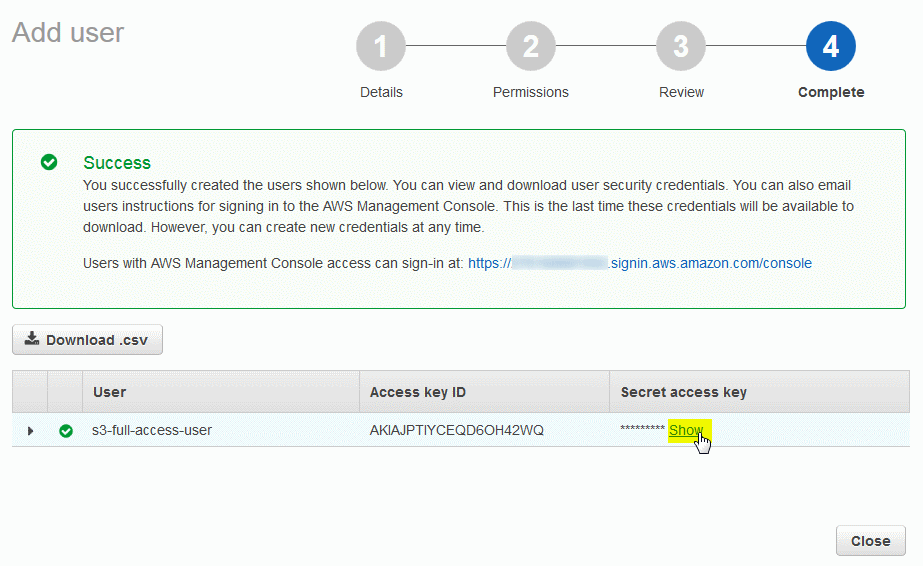
New User Created 11. Click Show under the Secret access key column 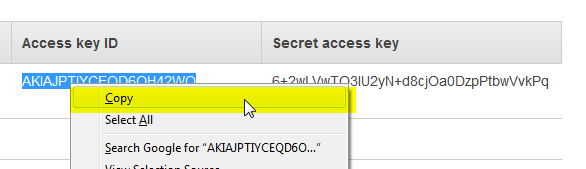
Copy Access Key Id And Secret Access Key 12. Copy Access key ID and Secret access key into the safe place. You can now use your access keys to add new Amazon S3 account to S3 Browser.
|